 重要提示:
请勿将账号共享给其他人使用,违者账号将被封禁!
重要提示:
请勿将账号共享给其他人使用,违者账号将被封禁!
题目
A. show ip links
B. show cdp neighbor
C. show cdp neighbor detail
D. show ip clients
E. show ip route
F. None of the above
 更多“You are logged into a router and with to view the layer 3 information about your neighbori”相关的问题
更多“You are logged into a router and with to view the layer 3 information about your neighbori”相关的问题
第1题
A.%
B.@
C.>
D.$
E.#
第2题
A.%
B.@
C.>
D.$
E.#
第3题
A.Directory Replication
B.Workstation
C.Netlogon
D.Server
第4题

A.A
B.B
C.C
D.D
第5题
.jpg)
You need to discover why users cannot modify data in the database, but you do not want to disrupt normal database activities. What should you do?
A.Use the spid 52 icon in the Current Activity window to discover which SQL statement is being executed
B.Use the sp_who stored procedure to discover who is logged in as spid 52
C.Use SQL Profiler to capture the activity of the user who is logged in as spid 52
D.Use System Monitor to log the locks that are granted in the database
第6题
A. Show ip protocols
B. Show ip route rip
C. Debug ip rip
D. Debug ip updates
E. Debug ip transactions
第7题
A.In the language in which you are logged on to the system
B.In the language of the purchase order header
C.In the language defined in the output determination Customizing settings
D.In the language defined in the vendor master record
第8题
A.By enabling the Slow Query Log because all queries that are not using indexes will be logged automatically
B.By enabling the Error Log because not using indexes is an error
C.By enabling the Slow Query Log and using the – log-queries-not-using-indexes option
D.By enabling the Error Log and using the – log-queries-not-using-indexes option
第9题
Your Windows Communication Foundation (WCF) client application uses HTTP to communicate with the service.You need to enable message logging and include all security information such as tokens and nonces in logged messages.What should you do?()
A.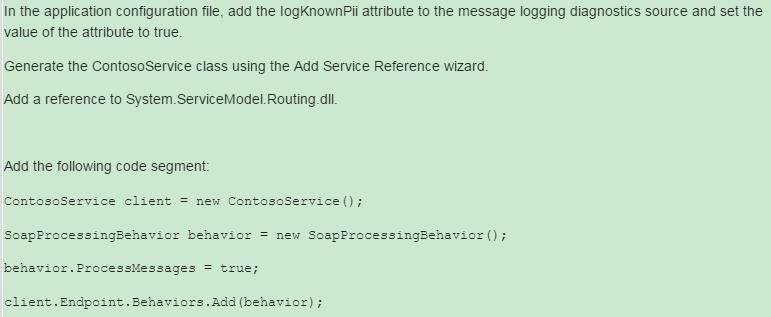
B.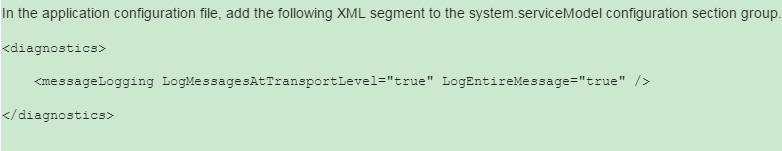
C.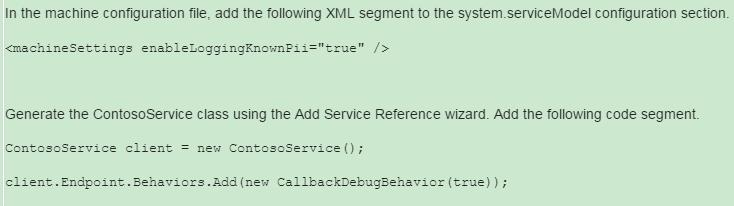
D.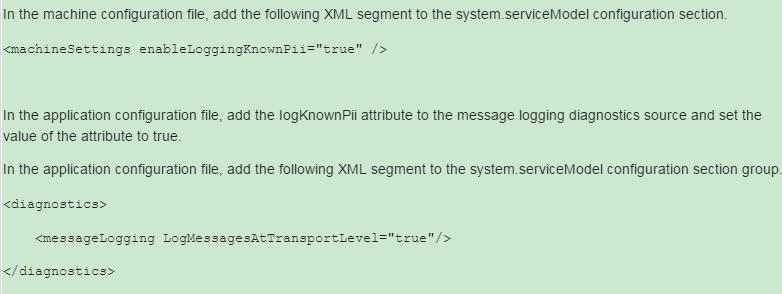
第10题
A. In the Web.config file, enable impersonation.
B. In IIS, enable anonymous access.
C. In IIS, disable anonymous access.
D. In the Web.config file, set the authentication mode to Windows.
第11题
A. The IP addresses of workstations allowed gain access to the router via an access list
B. Permanent name-to-address mappings created using the ip host command.
C. Temporary and permanent DNS entries.
D. The names of the routers created using the hostname command.
E. The length of time of users logged into the router, as well as the duration

 警告:系统检测到您的账号存在安全风险
警告:系统检测到您的账号存在安全风险
为了保护您的账号安全,请在“赏学吧”公众号进行验证,点击“官网服务”-“账号验证”后输入验证码“”完成验证,验证成功后方可继续查看答案!
